Introduction
“What the tools we rely on the most heavily have in common is that they’re all simple, durable, and ours.” – Lane Rettig, Ethereum Core Developer
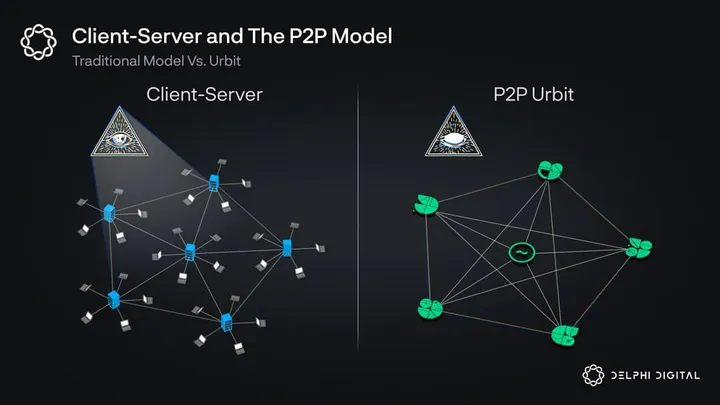
We have become cattle. The data of our online lives is constantly siphoned from us by a conglomerate of Web2 companies that sit at the center of the modern client-server network stack. When you go online, you first connect to a large Web2 company. These companies connect us to a larger world than our forebearers could ever grasp. But, these entities have used this central position to censor information and build an entire industry around surveillance capitalism. This existing client-server paradigm gives inordinate power to those who control the servers and have created the perverse incentives that have given rise to this problem. Unfortunately, there is little evidence to show that this trend is slowing, and with the advent of AI, it could very well accelerate. Now, more than ever, we are trapped in this paradigm and make it more potent the more data we give it.
It is this miserable state of affairs that Urbit seeks to disrupt. Urbit, in its end state, supplants the client-server relationship that has brought us to our increasingly dystopian relationship with the internet. Urbit’s vision is to create a fully P2P network of personal servers owned and operated by the people who use them. Rather than users accessing someone else’s servers when they go online, they would directly connect P2P with others on the network — completely removing the middlemen and the power that comes with them. Urbit’s goal is nothing short of completely supplanting the existing oligopoly of the Web2 internet with a more equitable, private, and open alternative.
The Design — OS, IDs, and Network
The final goal of Urbit would represent a fundamental shift in personal computing. The Urbit founders, including the controversial Curtis Yarvin (aka Mencius Moldbug), argue that we need to redesign the entire computing stack to account for the modern world in which we live. Existing operating systems like Windows or macOS harken to an age before the internet. These operating systems bolted-on network protocols to allow them to go online. Urbit’s founders argue that operating systems need to be designed with connectivity and privacy at the beginning, rather than adding these features onto systems designed for LANs or unconnected experiences.
As such, Urbit’s design has three main components: the OS itself, the persistent IDs, and the network protocol that creates their P2P network.
Operating System
Currently, for those with some technical know-how, the UX of using an Urbit instance is reasonably straightforward. You “host” the Urbit OS instance (also called a ship) on some device, and then you log into it through a web browser. For example, my Urbit is on a Raspberry Pi that I log into through Firefox. Like any other OS, I can add apps that allow me to customize the experience. There are apps for P2P video calls, file explorers, group managers, and more. The OS is lightweight and reasonably easy to use.
Each Urbit instance has its own unique ID. ID ownership is secured through Urbit’s PKI and the Azimuth smart contract on Ethereum. Urbit IDs themselves are NFTs secured with your private key. As long as you maintain the key, the Urbit ID is yours. Urbit instances are hardware-agnostic personal servers that users can migrate to new devices as long as they have the keys. As Urbit scales, the network can be populated by 4B unique IDs self-organizing into an encrypted, P2P permissionless internet. Urbit’s final stage is the manifestation of the cyberpunk ethos.
Persistent ID
The current suite of operating systems don’t offer any sort of persistent network presence. IP addresses change, MAC addresses can be spoofed, and VPNs are everywhere. This is great for privacy, but terrible for the current web’s Sybil resistance. Phishing, scams, and bots are commonplace on the internet, because if a bot address is discovered, they can freely move to another or make a new account on the platform.
Urbit, on the other hand, provides users with a persistent network ID. IDs on the Urbit network are limited and have an associated cost. This persistent ID forms an important part of the network’s Sybil resistance. If someone uses an Urbit ID for malicious purposes, other IDs on the Urbit network will refuse to connect with it. Without P2P connections on the Urbit network, the ID becomes essentially worthless, and the users will need to purchase a new one. Additionally, as IDs are persistent in Urbit, a user can migrate their Urbit ID to new devices and even pass their ID on to other people.
The Urbit Universe
 Like modern computers, Urbit instances become much more powerful when you connect with others — which, in Urbit’s case, is done P2P. Urbit’s P2P network is structured differently from other networks, and understanding it is key to grasping Urbit’s potential.
Like modern computers, Urbit instances become much more powerful when you connect with others — which, in Urbit’s case, is done P2P. Urbit’s P2P network is structured differently from other networks, and understanding it is key to grasping Urbit’s potential.
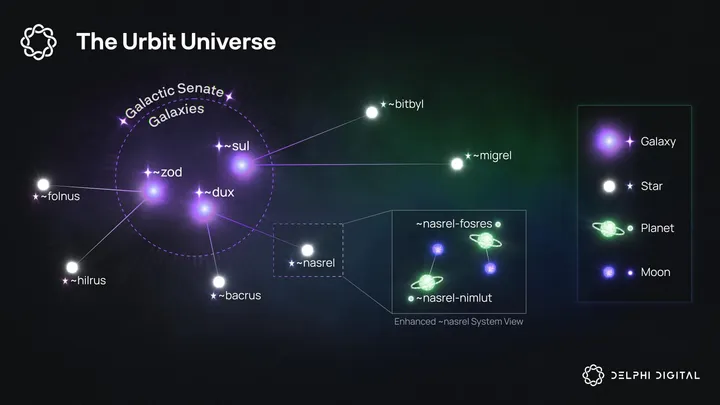
Urbit uses a unique hierarchical ID scheme for addressing and routing in place of the usual IP/DNS. At the center of the network are the Galaxies, followed by the Stars, Planets, Moons, and Comet IDs.
Each of these identities (aka ships) is just a simple base-256 number with a mnemonic name and sigil attached to it. The shorter the name, the shorter the number — the less complex the sigil, the shorter the number. More “powerful” identities have shorter names and smaller numbers. For example, the Galaxy ~dux is an 8-bit number, while a Planet ~nasrel-nimlut is 32-bit. The network uses these identities for packet routing and discovery on the network. An Urbit instance is like a ship floating around a celestial body, and its name (~nasrel-nimlut) is where it’s located in the Universe.
Urbit’s unique addressing scheme allows for ~4B unique identifiers on the network, not counting Moons and Comets. The hard cap on addresses is Urbit’s approach to Sybil resistance on the network. In their estimation, Sybil attacks (and spam) occur because identity is cheap on Web2 — you just need a computer and an internet connection to spam everyone else. By limiting Urbit’s address space, the identities gain a monetary value which reduces the likelihood of malicious use.
A Special Note on Sponsorship
An essential concept in the Urbit network is sponsorship. Urbit identities spawn other Urbit identities. The only Urbit ID to exist in the beginning was the prime Galaxy ~zod. The pri
Unlock Access
Gain complete access to in-depth analysis and actionable insights.
Tap into the industry’s most comprehensive research reports and media content on digital assets.
Be the first to discover exclusive opportunities & alpha
Understand the narratives driving the market
Build conviction with actionable, in-depth research reports
Engage with a community of leading investors & analysts
0 Comments
