Privacy Is Useful
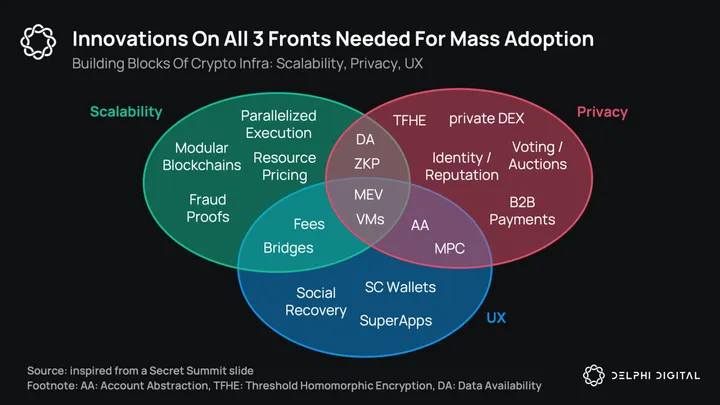
Blockchain infrastructure can be broadly summarized in three verticals: scalability, privacy, and UX. Due to high fees, most of our focus has historically been on scalability, and we covered UX in depth in our recent Wallet Wars report. Yet, to bring this technology to the masses, we really need innovations on all three fronts. In this post, we’re going to dive into privacy.
In August of 2022, the US Treasury sanctioned Tornado Cash citing money laundering concerns from cybercrime actors including North Korea-sponsored hacking group Lazarus. Following sanctions, certain Ethereum nodes and relayers in the US stopped processing blocks involving Tornado Cash txs. Due to Ethereum’s borderless nature, however, Tornado txs continue to find their way to the chain. As of today, anyone from the US still can’t legally use Tornado. Meanwhile, as an immutable smart contract on Ethereum, the application continues to operate. While the crypto community largely reacted and pushed back on OFAC’s decision, citing privacy as a human right, views on how to address privacy in the face of regulation differs. Recently, we also see new attempts to redesign Tornado in a regulatory-friendly way.
This report isn’t going to be a moral, ideological, or legal defense of privacy. If there is one source that does that better than anyone else, it is In Defense of Money Privacy. It covers this nuanced topic in depth and elegantly articulates why money laundering — often raised as a concern for private transfers — is a red herring.
We will, however, correct some straw man arguments such as “privacy is for criminals” or “you don’t need privacy if you have nothing to hide.” Privacy is part of our daily lives. Thanks to it, we can safely vote in elections, find relief in talk therapy, or go on with our lives knowing our bank balances aren’t visible to the world (as mandated by law). Privacy is normal. It enables us to be our authentic selves.
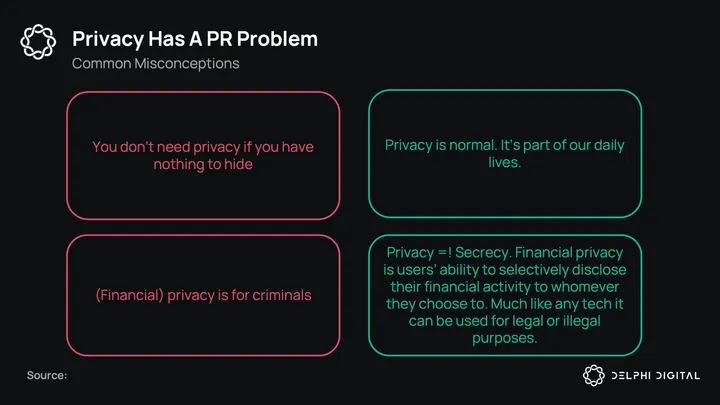
We leave ideological, moral arguments out of our scope; not because we don’t think they are important (they are!), but because we think “privacy for the sake of privacy” isn’t enough of a motivator for adoption. Acknowledging privacy’s importance is one thing, adopting it is another.
Today, the most adopted privacy technologies are VPNs and ad blockers, not because of ideological reasons, but simply because they are useful. VPNs allow people to get around geo-host restrictions and ad blockers save people’s precious time and attention. As with private dApps wanting to prioritize traction above all else, they need to be useful.
Luckily, it’s not very hard to find such useful cases in crypto given how constraining fully-transparent chains are. In most chains today, everyone can watch everyone. If you even make a single on-chain transfer to a friend, chances are, your friend will be able to not only see your entire transaction history, but also all your transactions in the future, forever. You will be eternally doxxed.
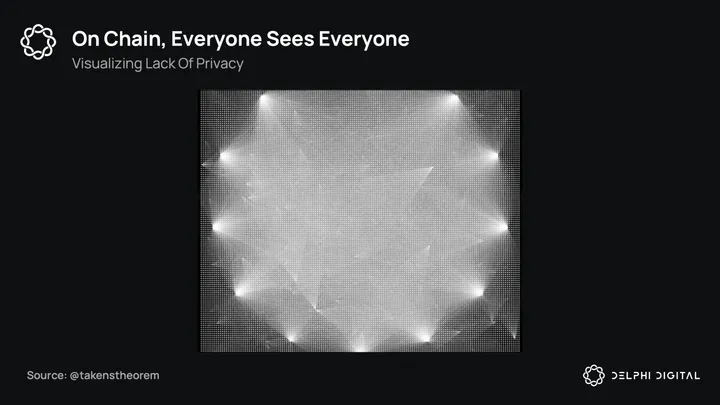
Let’s take a moment to realize what can’t be done on a fully transparent chain.
- Institutional adoption — considered to be the biggest demand driver for crypto — simply can’t materialize. Without privacy, businesses can’t and won’t perform their financial activities on-chain. That’s $40T of missed potential on B2B cross-border payments alone!
- On-chain reputation/credentials/identity systems — seen as the biggest use case after money — can’t scale.
- MEV remains a serious threat.
- Keeping DeFi free of manipulation is extremely difficult; copy trades, stop loss hunting, and highly profitable trading strategies are common.
- People can’t selectively disclose their NFTs.
- Any type of on-chain game that requires private user data (think fog of war games, hidden maps/prizes) or randomness is ruled out.
- Private voting, crowdfunding, auctions, airdrops, and donations are all ruled out (poor ConstitutionDAO gets outbid).
- Everyone continues to expose some of their most sensitive data — financial wealth — to the whole world, making them vulnerable to attacks not only in the digital world via scams, phishing etc., but also in the physical world.
The motivations for privacy are clear. Privacy can bring new use cases, scale existing ones, and in doing so, grow the value of the on-chain space by orders of magnitude.
Privacy Landscape
Blockchains have forever changed the course of cryptographic research. Despite regulatory concerns, funding in the privacy space has been significantly growing in recent years. An age-old field that historically received funding from no one besides the National Security Agency (NSA) continues to get VC funding like never before.
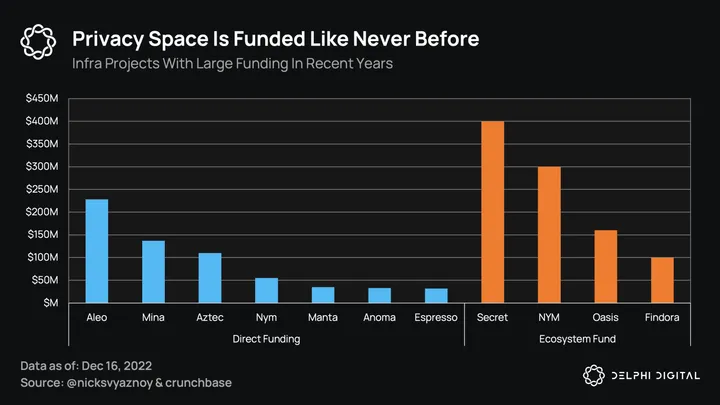
Today, there are 400+ projects spanning many verticals such as infra, DeFi, data transport, wallets, identity, messaging, social, etc. We break down some infra/DeFi projects below.
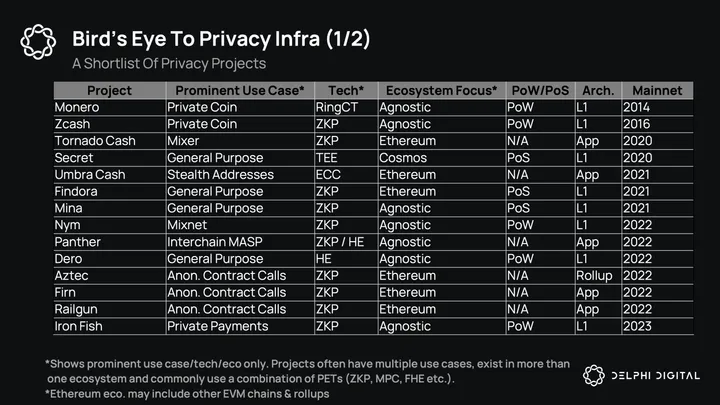
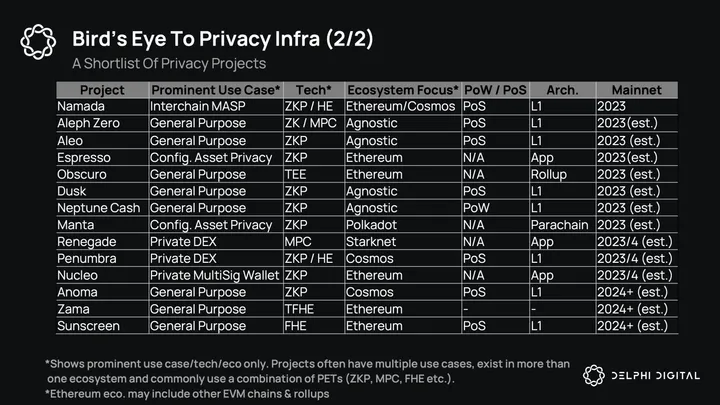
You’ll notice that use cases, technology, and architecture vary greatly from one project to another. With the exception of private coins/transfers — which are almost a decade old at this point — we still don’t have clarity on how to build private applications.
This begs the question: what is it that makes private applications so hard to build?
Privacy vs. Concurrent-Access-to-State
First, let’s identify the fundamental problem at hand.
Smart contract chains like Ethereum, Solana, etc. have a shared state model. An application’s state, like a Uniswap pool, often isn’t owned by any user but rather a smart contract that anyone can access and mutate by sending a transaction. All transactions are executed on-chain with a known order. As a result of this execution, the chain transitions from one state to another.
In contrast, private apps/chains require users to move at least some part of execution off-chain and perform it on the client side. After all, this is where privacy originates from. Nobody gets to know it’s happening.
Eventually, however, the effects of these private executions need to be recognized by everyone to advance the on-chain state. We need to settle these private executions.
This brings us to the heart of the problem — if different users all try to mutate a common pre-state on the client side, how can we ensure their off-chain state transitions don’t conflict with each other?
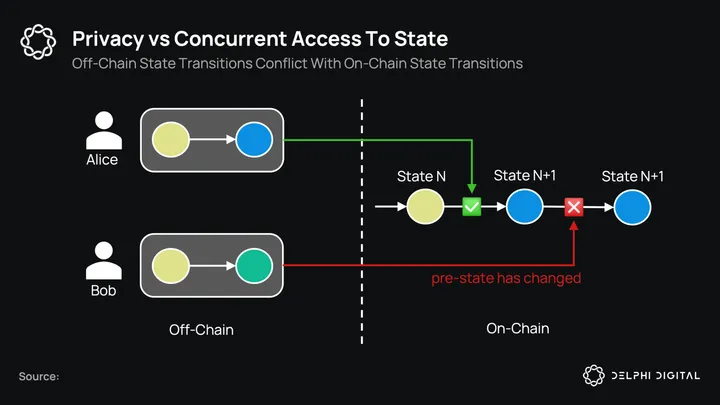
Notice the inherent dilemma here. Almost any interesting on-chain application requires some form of shared state between users. However, we can’t naively move execution over this shared state to the client side because it leads to race conditions between users. The first user to settle on-chain invalidates everyone else’s off-chain execution. Importantly, this is not an issue specific to a particular privacy-enabling tech (referred to as PET from here on), but a fundamental c
Unlock Access
Gain complete access to in-depth analysis and actionable insights.
Tap into the industry’s most comprehensive research reports and media content on digital assets.
Be the first to discover exclusive opportunities & alpha
Understand the narratives driving the market
Build conviction with actionable, in-depth research reports
Engage with a community of leading investors & analysts
0 Comments
