🌅 Welcome!
A former U.S. President is launching an NFT collection and a committee to represent creditors in the FTX bankruptcy case has been formed.
Today, we take a look at Valhalla while our Research team provides insights on prominent themes in web3 infrastructure.
This is the Delphi Daily. Let’s dive in.
🚨 In Case You Missed It
- Former U.S. President Donald Trump launches an NFT collection.
- A committee to represent creditors is formed in the FTX bankruptcy case.
- New York financial regulator issues crypto guidance for banks.
- SBF is “in good spirits” after spending his first night in a Bahamas prison.
- FTX Executive Ryan Salame tipped off regulators about FTX’s negligence.
📊 Valhalla Floor Price Surges After Armory Token Airdrop
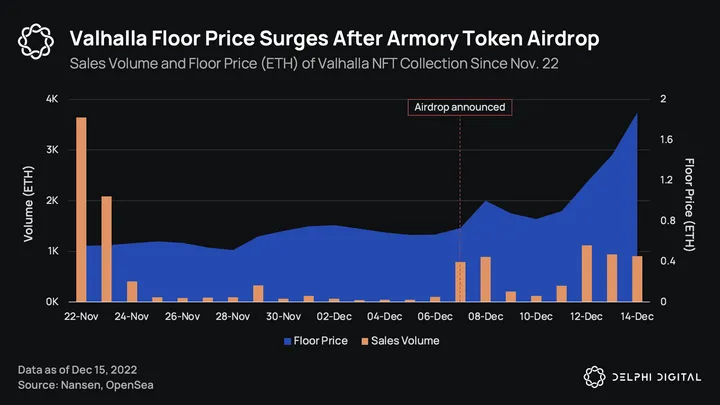
- Valhalla is a gaming and web3 culture-focused NFT collection, created by a Los Angeles-based startup called Stacked. On Dec. 7, the collection announced a token airdrop for the NFT holders.
- Holders will receive 5 tokens per NFT over the course of two weeks. The first token was airdropped on the day of the announcement itself. Since then, floor price has increased by 267% from an average of 0.7 ETH on Dec. 7 to an average of 1.87 ETH yesterday.
- Called Armory Tokens, holders can use them to re-roll specific Avatar traits. Re-rolling refers to updating the on-chain metadata of the user’s Avatar NFT. This action requires the user to burn the corresponding Armory Token as well.
- While these tokens do not expire, they can only be used during certain periods, with the first re-roll period occurring from Dec. 14 to Dec. 28. Once a trait is re-rolled, the change cannot be reversed.
- Valhalla has also introduced an event-only trait called “Chainsaw”, which will only be available for the next two weeks before being retired. The perceived scarcity has made this a highly sought-after trait.
⚡ The Year Ahead for Infrastructure
- When evaluating bridge designs, it’s tempting to see the security model and implementation as disjointed factors. However, moving forward, we would argue that the healthier (and perhaps more realistic) approach is to consider them in conjunction.
- At a high level, bridge designs can be categorized into three buckets: third party, light client, and rollup bridges. Third-party bridges are externally verified, while light client and rollup-based bridges are natively verified.
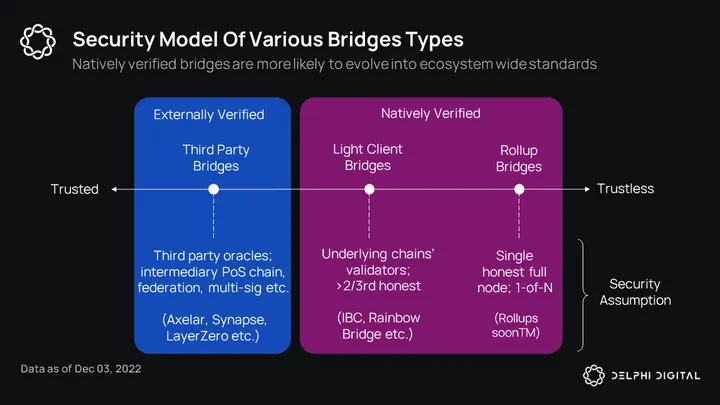
- Most bridges in the last two years have been externally verified bridges. These bridges are often developed and maintained by arbitrary teams each building their own designs. There is little to no cooperation between them in terms of code scrutiny.
- Furthermore, because they compete for market share, they are inclined to boost TVL by handing out rewards during the first few days of launch. This leads to a perfect environment for black hats.
- This is why we no longer think it’s a good idea to consider bridge designs in isolation from how they are likely to be implemented. We know by now that the threat model is nation state-level black hats.
- While we can never be certain that vulnerabilities don’t exist, the winning solutions are likely to be the ones that encourage maximum cooperation and code scrutiny. This brings us to natively verified bridges.
- The antidote for bridge hacks is standardization. Natively verified bridges (light client and rollup-based) have notable characteristics that make them more likely to evolve into standards than externally verified bridges.
- Natively verified bridges not only function as general message-passing protocols, but also serve other fundamental needs and primitives such as mobile wallets, fast syncing, reducing reliance on centralized RPC services, etc.
- Given that they are ecosystem-centric, natively verified bridges are relied upon and scrutinized by a larger number of teams and developers in their respective communities. Their roadmaps revolve around developing ecosystem-wide standards considering the maximum mutual benefit of ecosystem participants.
- Inarguably, the most successful example of this is IBC. IBC isn’t immune to implementation bugs, but its development greatly benefits from the mindshare and attention it receives from a large number of diverse Cosmos teams.
- Considering how a critical incident was flagged and patched recently, we can count this as an important factor for its survival.
- For more on prominent themes in web3 infrastructure, Delphi members can read our Delphi Pro report here.
🐣 Notable Tweets
Crypto UX
“crypto UX is too complicated”
Nouns Treasury
Lawyers of CT
Is this reasonable costs to setup a org structure for a project with a treasury?
Seems wild to me – how do most projects even get to hiring engineers if it costs $1.5M/y to simply exist?
-DCF GOD (@dcfgod)
0 Comments
