Report Summary
Summary of the Humanity Protocol Report
Humanity Protocol introduces a decentralized, privacy-preserving identity infrastructure tailored for the AI and Web3 era. Rather than just proving someone is human (proof-of-personhood), it enables selective, verifiable identity credentialing across education, finance, employment, and more — without compromising user data control or relying on centralized infrastructure.
Key Takeaways
1. Positioning vs. Worldcoin
-
Worldcoin: Centralized hardware (Orbs), biometric-only PoP, consumer-first, UBI-focused.
-
Humanity: Modular identity credentials, open validator network, developer-first, enterprise-grade SDKs.
-
Humanity aims to be horizontal identity infrastructure, not a consumer app.
2. Modular Identity System
-
Users collect and control credentials (e.g., diploma, bank history) in encrypted wallets.
-
Apps can request only specific data via zero-knowledge proofs (e.g., “is this user 18+?” without knowing exact age).
-
Supports both biometric verification (palm+vein scans) and credential stacking.
3. Privacy-First Architecture
-
All credentials and biometric templates are:
-
Stored on IPFS in encrypted, user-controlled formats.
-
Revocable and inaccessible without user consent.
-
-
zk-proofs allow apps to verify attributes without accessing raw data.
-
Users can opt out of biometrics entirely and still participate.
4. Tech Stack & Blockchain Design
-
Built as a zkEVM Layer-2 on Arbitrum, enabling:
-
Low fees, EVM compatibility, and cross-chain interoperability.
-
On-chain native credential verification logic (not just smart contracts).
-
-
May evolve into a standalone L1 as usage scales.
5. Credential Issuance & Verification Process
-
Validators: Issue credentials (e.g., universities, banks).
-
zkProofers: Generate privacy-preserving verification proofs.
-
Each request pays a fee in $H, split among validators, zkProofers, and the protocol.
6. zkTLS Extension
-
Enables users to verify web credentials (e.g., social logins, subscriptions) directly from browsers without third-party validators.
-
Expands Humanity’s reach into non-blockchain applications and common Web2 services.
7. Business Model & Token Utility ($H)
-
$H is used for:
-
Credential issuance (validators must stake $H).
-
Verification requests (apps pay in $H).
-
Delegated staking (users earn by backing trusted validators).
-
-
Fixed supply: 10B tokens; usage-based demand creates real utility.
-
However, token unlock/vesting transparency is currently lacking.
8. Governance & Control
-
Governance via $H tokens with Snapshot voting.
-
Human Institute still controls execution via multisig (3-of-5).
-
Clear roadmap for decentralization, but current structure retains centralized control and limited transparency on treasury oversight.
9. Traction & Roadmap
-
iOS/Android apps live, palm scans enabled.
-
Over 10M wallets and 8M+ Human IDs reserved.
-
Announced partners: Moongate (event ticketing), LayerZero, Kaito, OKX Wallet.
-
Token Generation Event ($H) launched June 25.
-
Upcoming:
-
DAO launch
-
Decentralized staking
-
Custom biometric hardware deployment
-
zkTLS browser extension
-
10. Risks & Open Questions
-
Token allocation opacity: Vesting schedule, Human Institute control unclear.
-
Governance gaps: No timeline for full decentralization, emergency powers unchecked.
-
Incentive viability: Credential pricing, app demand, and validator economics unproven at scale.
Conclusion
Humanity Protocol is building the most comprehensive, privacy-preserving identity layer in crypto — beyond PoP, toward selective, verifiable digital identity. It avoids the pitfalls of hardware-heavy systems (like Worldcoin), leverages zk-proofs and modular credentialing, and focuses on practical enterprise integrations.
While technical execution and demand validation look promising, tokenomics clarity and governance decentralization are essential next steps. Humanity could become the core identity rail for Web3 and AI-native internet — but it must maintain trust and transparency as it scales.
-
Intro / TLDR
Every major technological primitive goes through cycles of maturation. Web browsers evolved from text-based interfaces to immersive multimedia experiences, payment systems transformed from physical transactions to instant digital transfers, social networks progressed from basic messaging to complex algorithmic content curation. Each breakthrough solved critical coordination problems that enabled subsequent waves of innovation.
Identity now stands as one of the next essential primitives for the internet’s continued evolution.
As AI continues to accelerate and synthetic content becomes indistinguishable from human creation, the ability to provide comprehensive, verifiable identity signals will determine which companies can maintain authentic human usage rather than being overwhelmed by algorithmic manipulation and fraud. Since anyone can now generate thousands of convincing, fraudulent personas across virtual and physical environments, the need for a decentralized identity (DiD) solution is clear.
While the identity challenge manifests itself across all digital platforms, crypto provides the only viable infrastructure to solve it at scale. Traditional centralized systems can’t deliver the privacy-preserving, user-controlled verification that modern trust requirements demand – which is why a16z has identified identity as one of four critical components at the intersection of crypto and AI.
Humanity Protocol introduces a composable identity infrastructure that transcends proof-of-personhood (PoP). Instead of simply proving unique human status, users can selectively demonstrate specific attributes like educational credentials, financial capacity, or professional expertise, all while preserving privacy. The solution’s modular design enables selective credential verification across digital applications, physical infrastructure, and hybrid environments. Users control exactly which attributes they reveal for each interaction.
Current attempts may address immediate sybil resistance needs – as we explored in my recent World report – but they lack the breadth of personalization that powers modern experiences across Web2, Web3, and real-world interactions.
In this report, we’ll discuss Humanity Protocol’s technical architecture, economic model, and scaling strategy while addressing the questions:
How is Humanity’s approach different from World’s?
Can we trust them?
What will their business model look like and will it create sustainable token value?
Humanity vs. World: Strategic Divergence
While World has spearheaded awareness of the need for PoP, Humanity benefits from entering the identity space with valuable learnings as a second mover. This advantage manifests itself across scalability, market positioning, and long term value creation.
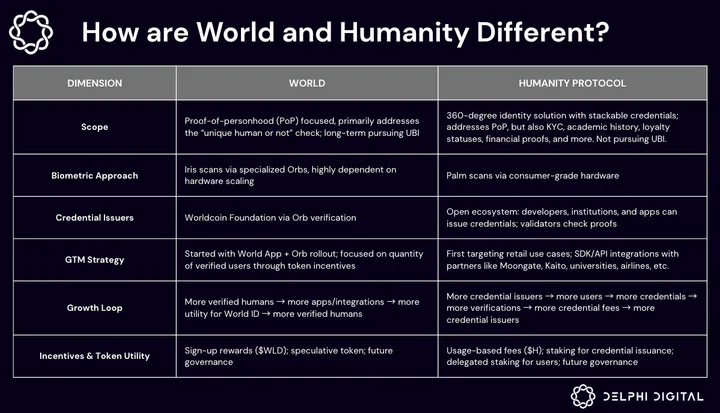
Let’s take a closer look at the dimensions highlighted above.
Scope: Binary vs. Comprehensive Identity Solution
World: Focuses exclusively on PoP (unique human or not) while pursuing UBI distribution. This narrow scope solves immediate sybil resistance but limits monetization to one use case. The focus on UBI is heavily dependent on network effects, requiring massive user adoption before generating meaningful utility (i.e., the network won’t be valuable if only 1M people are verified as real humans).
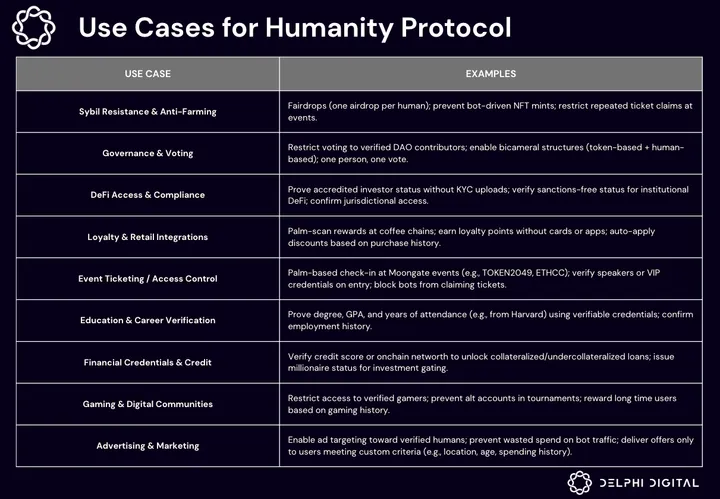
Humanity: Delivers a comprehensive identity solution with stackable credentials that provide real utility from day one. The breadth of practical use cases (highlighted in the visual below) not only allows Humanity to generate immediate value for users and applications regardless of network size, but substantially increases their total addressable market.
 Humanity’s spectrum of identity offerings is complemented by modularity, unlocking alternative pathways to human verification beyond biometrics. Rather than requiring palm scans to prove uniqueness, users can combine verifications from various sources to establish human authenticity. For example, you might combine credentials that prove: (1) you have several years of Grubhub transaction history, (2) you have an account with Chase bank, and (3) you have a diploma from Harvard University.
Humanity’s spectrum of identity offerings is complemented by modularity, unlocking alternative pathways to human verification beyond biometrics. Rather than requiring palm scans to prove uniqueness, users can combine verifications from various sources to establish human authenticity. For example, you might combine credentials that prove: (1) you have several years of Grubhub transaction history, (2) you have an account with Chase bank, and (3) you have a diploma from Harvard University.
Of course, this may be slightly less robust than direct biometric verification, but this multi-credential approach creates exponentially higher fraud barriers than most current solutions while dramatically improving accessibility and user adoption.
Hardware Dependency vs. Scaling Flexibility
World: Biometric scanning via specialized Orbs create scaling constraints. The required manufacturing, distribution, and maintenance of hardware requires enormous capital investment while creating multiple single points of failure.
Humanity: Two points here.
- Palm scans can be done via smartphones or optional dedicated scanners, reducing dependence on centralized manufacturing and removing geographic constraints from the verification process. (i.e., no need for users to be in a specific place to access specialized hardware).
- Alternative methods for proving uniqueness (such as stacking credentials, which will be explained later) are supported.
These features remove hardware dependency as a growth constraint and represent a classic “need-to-believe” versus “nice-to-have” distinction. World requires expensive Orb deployment, reliable hardware operations, and user willingness to visit specific locations, while Humanity only requires software adoption, making scaling probability significantly higher through fewer dependencies.
Credential Issuers: Centralized vs. Distributed Trust Architecture
World: The World Foundation maintains exclusive credential issuance authority through its proprietary Orb hardware. While ensuring consistency (which may be better for biometric scanning), this centralization limits credential diversity and makes the ecosystem dependent on a single verification mechanism and issuer.
Humanity: Open ecosystem enabling developers, institutions, and applications to issue specialized credentials. Universities can verify degrees, banks can confirm financial status, and gaming platforms can validate historical achievements.
This distributed approach creates powerful network effects – each new credential issuer increases platform utility for all existing users, while credential diversity attracts applications requiring specific verification types that World can’t provide.
GTM Strategy: Consumer Subsidies vs. Immediate Use-Cases
World: Consumer-first approach through World App and Orb rollout, incentivizing adoption through direct token payments. This strategy requires substantial upfront capital while counting on enterprise applications to integrate as the network scales.
Humanity: Developer-first strategy targeting enterprise use cases through SDK/API integrations. Early partnerships with Moongate (event ticketing), universities (academic credentials), and financial institutions create immediate revenue streams while building organic user acquisition.
Incentives & Token Utility: Speculative vs. Functional
World: Verification rewards (distributed in $WLD) create speculative token mechanics with uncertain long-term sustainability. Users receive tokens for verification but unclear ongoing utility beyond potential governance participation.
Humanity: Usage-based fee structure (paid in $H) generates immediate protocol revenue. Apps pay for credential verification, validators stake tokens for issuance rights, and users delegate stakes to trusted issuers, creating functional token demand that scales with adoption.
This is a clear distinction in economic models. World optimizes for rapid user acquisition hoping monetization eventually follows, while Humanity builds sustainable revenue mechanisms and token utility that supports organic growth from launch.
Summing it Up
These differences reveal that Humanity might not be directly competing with World.
World functions as a vertically integrated consumer application, controlling hardware, verification processes, and user experience to build a unified identity ecosystem. This approach targets mass consumer adoption through direct incentives.
But on the other hand, Humanity operates as horizontal developer infrastructure, providing APIs and verification tools for other applications to build upon. Rather than pursuing the same consumer base, Humanity first targets enterprises, institutions, and developers who need specialized credential verification capabilities.
Where World pioneered market awareness and absorbed regulatory scrutiny, Humanity designed solutions that systematically avoid these constraints. Think market segmentation rather than market competition, with each protocol serving distinct use cases within the broader identity verification landscape.
What is Humanity Building?
Humanity enables users to collect and control verified digital certificates that prove specific attributes about themselves. These credentials are tamper-proof digital documents – university degrees, bank account confirmations, professional certifications, etc. – that users own permanently and can share selectively.
The system works through a simple flow: specialized organizations issue credentials within their areas of expertise, users store these credentials in encrypted digital wallets, and apps can verify specific attributes without accessing complete personal profiles. A user might prove they graduated from X university without revealing which school, when they graduated, or their GPA (you could choose to share all of this information if you want).
This credential framework creates unprecedented flexibility for digital identity. Every credential verification requires explicit user approval, and apps must request specific attributes and receive only the minimum information necessary for their use case. This selective disclosure ensures users never share more personal data than required.
Now that you have a basic understanding of what Humanity is, let’s take a closer look at the mechanisms that make their vision possible.
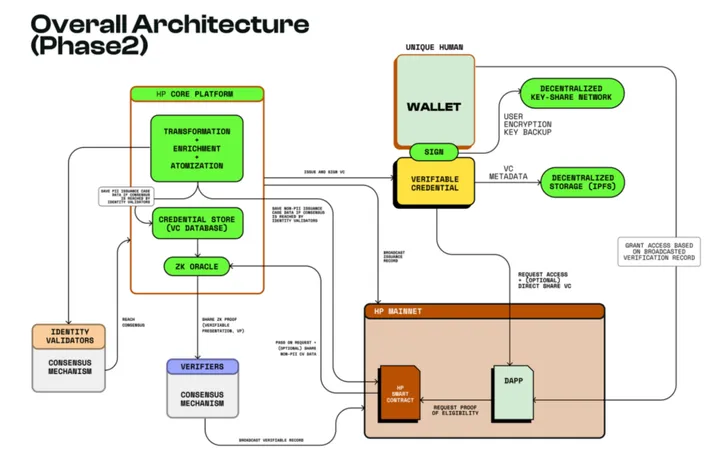
Blockchain Layer
Humanity Protocol operates as a zkEVM L2 solution built on Arbitrum, providing the scalability and cost efficiency necessary for high-frequency credential verification while maintaining Ethereum security guarantees.
This L2 approach offers several advantages for identity infrastructure:
- Transaction costs remain low enough to support micro-payments for credential verification, while throughput scales to handle millions of daily verification requests.
- EVM compatibility enables seamless integration with existing Ethereum tooling and developer frameworks.
- Native credential functionality gets embedded directly into the blockchain layer rather than implemented through smart contracts alone, optimizing gas efficiency for credential operations while enabling more sophisticated verification logic than traditional contract-based approaches.
- Cross-chain interoperability allows credential verification across multiple blockchain networks. Apps built on Ethereum, Polygon, or other EVM-compatible chains can verify Humanity credentials through bridge infrastructure, expanding the addressable market beyond a single blockchain ecosystem.
Humanity may look to build their own dedicated L1 in the future. As credential verification volume grows and requires more specialized consensus mechanisms, migrating to a purpose-built blockchain could offer additional performance optimization and governance capabilities tailored specifically for identity verification.
Biometric Verification
Humanity combines palm print analysis with palm+vein recognition to create a dual-layer biometric system that significantly outperforms other widely used scanning methods used for PoP. Here it is in action:
Doesn’t get easier than this: wave your palm, and you’re IN! 🖐️@TK_Humanity showcasing the tech for @scottmelker, @ysiu highlighting the benefits. pic.twitter.com/TPUEAEoH6T
— Humanity Protocol 「 🖐️ ✦ 🇺🇳 」 (@Humanityprot) June 3, 2025
The process may look simple on the surface, but under the surface, palm scans capture ridge patterns and geometric features, while infrared sensors map the unique blood vessel patterns beneath the skin.
Why use palm+vein scanning over alternatives?
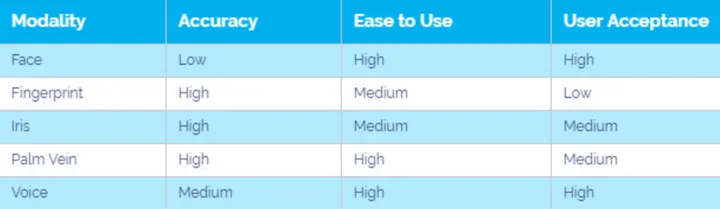
It’s less intrusive. Palm+vein verification operates at comfortable distances without requiring chin rests, precise eye positioning, or close contact with shared hardware. Users simply hold their hand naturally toward a sensor, significantly eliminating the positioning challenges and hygiene concerns associated with iris/face scanners. This intuitive experience creates a better user experience that encourages adoption.
It’s more reliable long-term. Vein patterns remain completely stable throughout an individual’s lifetime, unaffected by aging, facial changes, glasses, or other appearance modifications that compromise facial recognition systems. This stability reduces re-enrollment requirements and maintains verification accuracy over decades, making it ideal for PoP systems that must function reliably across extended time periods.
It’s easier to deploy and scale. Palm print recognition can be performed via smartphone cameras, while vein scanning requires near-infrared (NIR) sensors for subdermal mapping. Humanity’s system supports both, offering a flexible upgrade path depending on device capability and use case. Even when enhanced vein scanning is desired, Humanity’s specialized NIR hardware is significantly cheaper and easier to manufacture than other biometric scanners. This modular approach for biometric scanning enables broad initial deployment through existing smartphone infrastructure while providing clear upgrade pathways. Humanity’s architecture also supports efficient 1:N matching against large databases, enabling real-time verification across millions of users without performance degradation.
Last but not least, it’s harder to spoof. Palm+vein patterns exist beneath the skin surface, requiring active blood circulation for detection. This subdermal requirement provides stronger anti-spoofing protection than iris scanning, which can potentially be compromised through contact lens attacks.The infrared-based vein mapping cannot be replicated through photographs, masks, or external devices.
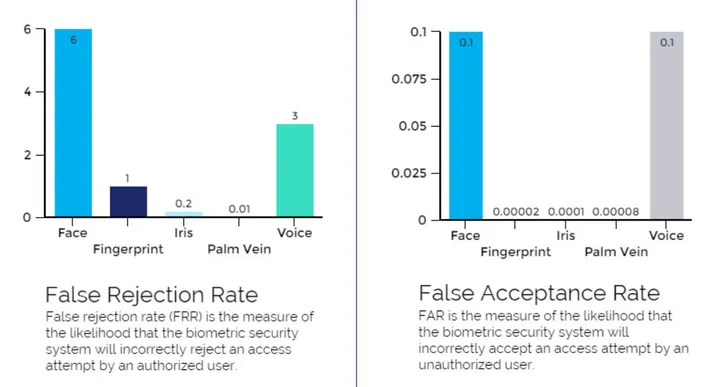
As shown in the visual above (and explained here), palm+vein systems achieve the best accuracy metrics out of the top five most widely used biometric scanning techniques.
While palm+vein scanning provides the highest accuracy and security, I want to emphasize that (1) they require specialized hardware and (2) Humanity makes them optional.
Humanity also supports onboarding via consumer-device palm scans (which are less robust than palm+vein scans with dedicated devices, but still accurate) and additional methods of verification (social media accounts, email, education, credential stacking, etc.), ensuring greater accessibility.
Credential Verification: Identity Validators & zkProofers
Humanity’s verification process is powered by two specialized network actors working in tandem – one focused on issuing trustworthy credentials, the other on verifying them without compromising user privacy.
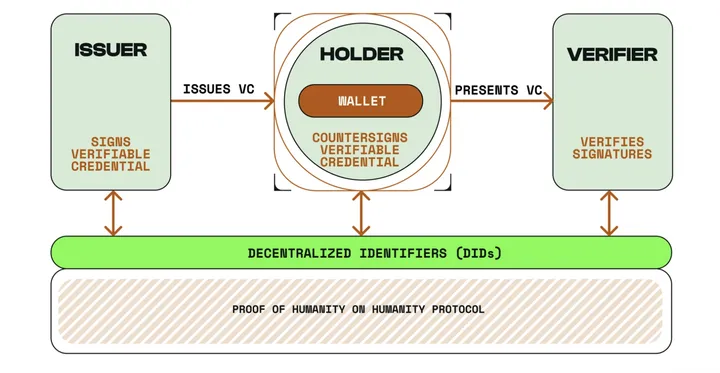
We’ll start with identity validators. These are the credential issuers, the trusted organizations that issue digital credentials within their areas of expertise (academic institutions validate education history, companies verify employment history, banks confirm balance or transaction history). They function like official document issuers in the physical world.
These entities might become validators for two reasons. First, it provides a secure way to verify their credentials without handling ongoing verification requests. Instead of fielding hundreds of calls from employers checking degrees, Harvard issues one digital credential that employers can verify instantly. While this eliminates administrative overhead, identity validators are also incentivized by monetary rewards for handing out credentials (more on this in the business model section).
Once validators issue credentials, zkProofers handle all verification requests while maintaining complete user privacy. Think of zkProofers like bank tellers who can confirm you have sufficient funds for a purchase without revealing your exact account balance or financial history to the merchant.
Here’s what the process looks like in practice:
- Request Processing: Apps submit credential verification requests to zkProofers, who work with Humanity’s sequencer to organize these requests into secure batches with unique digital fingerprints.
- zk-Proof Generation: zkProofers examine user credentials and generate mathematical proofs that confirm validity without accessing or exposing the underlying personal data.
- Distributed Validation: Multiple independent nodes review each batch and provide signatures confirming proof integrity.
- Result Delivery: zkProofers record verification results onchain for permanent documentation, then return simple yes/no answers to requesting applications with cryptographic authenticity proof.
zkProofers earn $H tokens for verification services, creating direct economic incentives for maintaining high-quality proof generation and network security. This distributed compensation model ensures no single entity controls the verification process while maintaining service reliability.
The network design makes large-scale fraud extremely difficult through multiple protection layers:
- Creating fake credentials requires compromising established institutions like universities or banks.
- Verification fraud demands complex coordination of simultaneous attacks across multiple independent zkProofer nodes and validation systems.
Together, identity validators and zkProofers form the core credentialing layer of Humanity’s architecture. While zkProofers enable verifiable trust without exposing data, the protocol’s deeper privacy architecture – including user control, encrypted storage, and granular credential disclosure – is addressed in the following section (Can We Trust Humanity?).
zkTLS Extension
Beyond institutional validators and biometric verification, Humanity is developing additional credentialing mechanisms that minimize the reliance on external parties. The zkTLS (zero-knowledge Transport Layer Security) extension will enable users to generate verified credentials directly from their browser without needing universities, banks, or other organizations to participate as active validators.
This feature leverages existing web infrastructure to create cryptographic proofs of digital relationships, profiles, and activities. Users can prove website login credentials or account status without exposing actual login information to Humanity or other third parties. For example, you might use this to:
- Prove your gaming achievements by logging into your Playstation Network or Xbox Live profile
- Confirm current streaming subscriptions by logging into Netflix, Disney+, Hulu, etc.
- Validate social media reach by logging into your Instagram, TikTok, or X account
zkTLS generates cryptographic proofs directly through browser connections to those websites. Unlike traditional verification methods that require sharing comprehensive account information, zkTLS enables selective disclosure of specific attributes without exposing detailed personal data. This approach demonstrates Humanity’s commitment to practical accessibility through familiar interfaces that don’t require specialized hardware investments.
Dev Tooling
Humanity’s development framework provides REST APIs and SDKs that abstract complex identity verification into easy-to-use tools that any app can integrate. Think of it like a simple on/off switch: devs ask “Does this user have a valid university degree?” and receive a clear yes/no answer with mathematical proof of authenticity.
Integration requires minimal technical expertise through pre-built software libraries that work with popular programming languages like Python, JavaScript, and Go. These tools handle all the complicated background processes – biometric verification, cryptographic proof generation, and secure data storage – automatically.
This simplified approach removes technical barriers while maintaining enterprise-grade security. Devs can interact with identity verification like any other web2 service without needing expertise in things like zk or distributed systems.
Can We Trust Humanity?
Now let’s pivot to privacy and security.
Given the risks of censorship, breaches, and misuse, handing over personal data to any identity system demands real scrutiny. Protocols can’t just have good intentions – they need architectural guarantees.
Historically, these identity systems just ask you to trust them. Humanity Protocol doesn’t. It’s architected so that users don’t have to trust any single company, server, or validator. The protocol enforces data privacy through encryption, decentralization, and user-level control over what gets stored, where, and for how long.
What’s Collected and How is it Handled?
The core of Humanity’s privacy model is local-first, designed to collect only the minimum data necessary for verification and to give users full control over who can see it, where it’s stored, and how it’s used. While some data is necessary to issue and prove credentials, the vast majority remains private, local, and user-controlled.
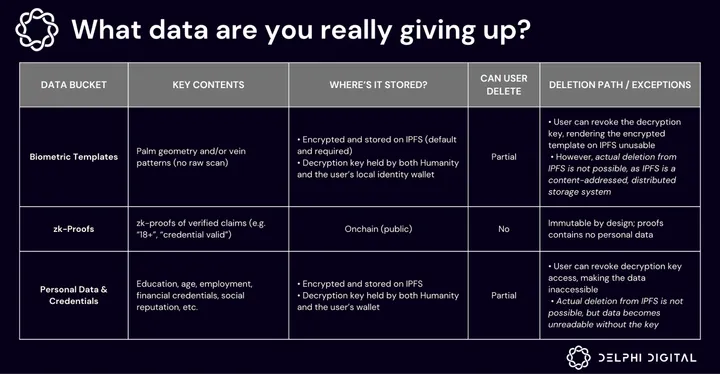 There are generally three categories of data handled by the system: biometric templates, zk-proofs, and user-controlled personal data.
There are generally three categories of data handled by the system: biometric templates, zk-proofs, and user-controlled personal data.
Biometric templates (optional) are only collected if the user chooses to enroll via palm scan. As previously mentioned, this method captures palm print geometry and subdermal vein patterns, which are both processed locally on the user’s device to generate a unique identifier. The raw scan is never uploaded anywhere.
To ensure users don’t lose access to their palm-based credentials if their device is lost or damaged, Humanity encrypts these biometric templates (the extracted and encrypted features) and uploads them to IPFS. Before uploading to this decentralized file system, each biometric template is split into multiple encrypted pieces that are stored separately across the IPFS nodes.
The decryption key is held both by Humanity and the user’s wallet, allowing secure recovery when needed. This key is revocable and user-controlled, meaning users can revoke Humanity’s access at any time. Humanity uses Lit Protocol for this decentralized key storage.
Without this key, the encrypted biometric data stored on IPFS is unreadable and cannot be reconstructed, even if accessed by a third party.
With that said, this biometric step is optional and not required to participate in the protocol.
Zk-proofs are the cryptographic attestations that confirm a credential is valid without revealing the underlying data. When you initiate a credential verification:
- Your local identity wallet generates a zk-proof in response to the request.
- This proof is then processed by zkProofers who verify its mathematical validity without accessing or viewing any underlying personal data.
- The proof is batched and recorded by the network sequencer, and the requesting application receives only a yes/no answer along with a cryptographic attestation.
At no point can zkProofers, identity validators, or applications see the raw credential data being verified. None of these actors can retain data after verification is completed and each proof is processed statelessly, meaning there’s no caching or storage of the credentials being verified.
Since they’re stored onchain, zk-proofs are publicly visible, but contain no personally identifiable information. They only confirm that a claim has been verified (such as “someone meets the age requirement”) without revealing who they are or any additional personal data.
To make sure credentials still exist and haven’t been tampered with, Humanity gives the option to store non-sensitive credential metadata to IPFS – this includes things like credential type (e.g., degree income verification), issuer category (e.g., university, financial institution), and expiration or revocation status.
Personal data and credentials (e.g., your verified age, education, employment, financial status, or other identity attributes) are encrypted and also stored on IPFS to ensure decentralized availability and recoverability. No one can see this data except you – no app, validator, or protocol participant can access it unless you explicitly grant permission through a verification request. This is mandatory if you want to use credential-based verification services, but you choose which credentials to store, verify, or share. Humanity never stores this data in a centralized location.
IPFS is also used to anchor tamper-resistant references to non-sensitive credential data. This includes hashed credential identifiers and minimal schema information such as credential type, issuer category, and expiration parameters.
Unlike traditional identity systems where governments or insiders can access private records through subpoenas, hacks, or leaks, Humanity’s model removes the administrative attack surface entirely. See the below for a breakdown of traditional data protection pitfalls, and how Humanity protects against them:
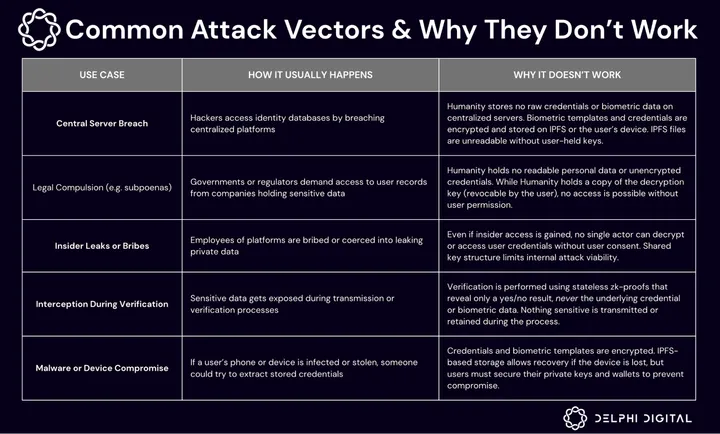
The bottom line: No data is stored on centralized servers and there is no single party that can be compelled, breached, or bribed to extract user information.
Can You Delete Your Data?
Short answer – not exactly.
Humanity doesn’t offer full technical erasure (like deleting from a centralized server), but it does offer meaningful control: users can revoke access to encrypted data, making it permanently unusable. This applies to both biometric templates and personal credentials stored on IPFS.
Since IPFS is a decentralized file system, published data can’t be force-deleted from every node. However, that doesn’t mean the data remains usable. Since Humanity’s encryption model requires the decryption key (held by both the user’s wallet and Humanity), revoking this key renders the encrypted data fragments inaccessible. In effect, they become permanent garbage – still technically present, but impossible to reconstruct or read.
zk-proofs of credential verifications also can’t be deleted as they’re stored onchain. However, they contain no personally identifying information and reveal nothing beyond the fact that a credential claim was successfully verified at a specific point in time (e.g. “a user is over 18” or “a valid university credential was checked”). This is why Humanity does not promise “total erasure” of all traces that a credential or biometric scan once existed.
In short, while full deletion in the traditional sense isn’t possible, Humanity’s architecture provides users with cryptographic control over their data. You can’t erase every trace, but you can make it impossible for anyone, including Humanity, to ever access your data again. This level of data sovereignty aligns with global privacy standards like GDPR and CCPA, while acknowledging the technical realities of decentralized storage.
Verdict on Trust
Humanity assumes worst-case behavior from all participants and still protects the user.
No central authority can access or revoke your credentials. No validator can see your biometric template. No app can learn more than you explicitly choose to reveal. There is no hidden storage, no behavioral profiling, and no backdoor.
These comprehensive user data protections are what make Humanity’s privacy model different. It’s not just a layer of encryption wrapped around centralized infrastructure – it’s a system where users truly own their identity.
Just as important, Humanity doesn’t force users into a single path.
If you’re uncomfortable sharing biometric data, you can still use third-party credentials. If you don’t want to anchor anything on IPFS, you can still verify your identity locally. The system is modular – you opt into the data types and verification methods that make sense for your use case. That makes Humanity far more practical than “all-or-nothing” identity systems.
Humanity doesn’t force you into handing over any data, so you don’t have to trust every component to benefit from the parts that matter to you.
Business Model & Tokenomics: Utility > Speculation
It seems we can trust Humanity in handling our data, but can we trust the protocol’s economic structure?
From the information that’s publicly available, Humanity’s economic model is grounded in real usage and utility. The native token, $H, is integrated into the protocol’s credentialing and verification infrastructure, governing access, funding critical work, and aligning the incentives of all network participants.
The result is a system where value accrues as a direct function of activity: the more credentials issued and verified, the more $H is demanded, circulated, and earned.
Value Capture & Revenue
Let’s talk about how this works.
Credential Issuance: To issue credentials on Humanity, the identity validators must first stake $H. This is a permissionless but capital-sensitive process, ensuring validators are incentivized to issue high-quality, fraud-resistant credentials.
Poorly issued credentials damage a validator’s reputation and directly impact their earnings. Because verification fees are only paid when credentials are used and accepted by 3rd-party apps, validators are economically incentivized to issue high-quality, widely accepted credentials. Inactive or frequently ignored credentials reduce revenue, while serious abuse may result in slashing or removal.
While the exact rules for slashing and credential rejection thresholds have not yet been disclosed, this reputation-based system aligns validator rewards with real-world credential utility.
Verification: When a third party (e.g., apps, DAOs, employers) wants to verify a user’s credential, they submit a verification request through Humanity. Each of these requests require the payment of a small fee in $H, establishing demand-side pressure for the token. Each verification fee is split between:
- Identity Validators– rewarded for issuing the credential being verified.
- zkProofers – rewarded for computing and validating the proof of authenticity.
- Humanity Protocol – a portion is routed to the network to fund future development, grants, and sustainability initiatives.
As of this report, the specific percentage allocations for validators, zkProofers, and the protocol treasury have not been disclosed – but the high-level design is clear. The token captures value from protocol usage, and rewards flow to the entities performing useful, verifiable work.
Delegated Staking: Most users won’t run their own validator or zkProofer nodes, but Humanity still allows them to participate in credential issuance through delegated staking.
The feature allows holders to delegate their $H to specific identity validators, effectively “vouching” for their trustworthiness. In return, they earn a share of the validator’s revenue from credential issuance and verification activity. This expands network participation without compromising security, and gives passive tokenholders a role in shaping which validators succeed.
Validators with more delegated stake are more likely to be selected for credential issuance roles, creating a network-native reputation system driven by user capital and real-world credibility.
Tokenomics ($H)
Humanity has confirmed that $H will have a fixed supply of 10 billion tokens, allocated across several categories to fund ecosystem growth, community participation, and protocol development, as follows:
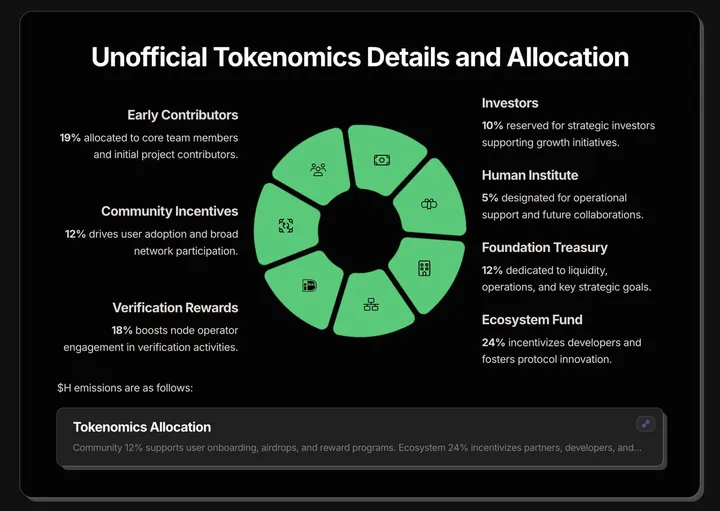
The most important missing detail is the vesting and unlock schedule for early contributors and investors. Without this, it’s difficult to evaluate the potential sell pressure or timeline of token dilution. A long-term vesting plan (e.g., 3-5 years with a meaningful cliff) would be a positive sign of alignment, but this remains unknown as of this report.
Additionally, the combined 29% of the supply is allocated to early contributors and investors. This is high, but not unusual compared to other recent, high-profile crypto projects. The detail to look out for is that some protocols attempt to obscure these allocations by routing them through intermediary entities (e.g., foundations or ecosystem development funds).
In Humanity’s case, the Human Institute (the above screenshot shows the extent of what’s included in their website… see for yourself) – the organization behind the protocol’s development – has not yet publicly disclosed how its token allocation compares to or overlaps with the foundation treasury. This lack of clarity makes it difficult to assess how much discretion the core team will have over future funding, and what governance constraints (if any) will apply to this portion of tokens. More transparency here would help clarify the project’s long-term alignment with community interests.
Overall, Humanity’s token distribution appears within industry norms in raw percentage terms, but greater transparency around vesting terms, Human Institute + foundation treasury discretion, and governance mechanics will be crucial to evaluating the long-term sustainability and decentralization of the protocol.
Governance Architecture
What’s an identity solution without proper governance structures in place?
Humanity’s governance framework is active in its initial phase and designed for progressive decentralization. $H tokenholders can vote on protocol upgrades, validator rules, and treasury allocations. Some important things to know:
- Proposal submission: Any tokenholder may draft a proposal. To submit formally, users must hold at least 100,000 $H or receive community endorsement.
- For a vote to pass: (1) at least 10M $H must participate, and (2) among voting tokens, at least 50% must vote “yes”
- Execution: Once a proposal passes, the Human Institute uses a 3-out-of-5 multisig wallet to carry it out. This usually happens within 7 days. The Human Institute can’t block or change approved proposals.
- Transparency: All voting history, validator lists, treasury wallets, and upgrade schedules are published on-chain and on GitHub.
The governance process includes a 5 to 10 day discussion period voting begins. While off-chain voting is currently used (via Snapshot), execution is enforced manually through Human Institute’s multisig.
While the initial design is promising, several critical governance details remain unresolved, especially around long-term control and transition timing (we will discuss more about these questions later).
Traction & Roadmap
Humanity Protocol has advanced rapidly from testnet rollouts to real-world utility, demonstrating growing engagement and strategic milestones across app launches, events, and incentive mechanisms.
What’s Live Now
- iOS & Android App: The Android version launched June 17, and the iOS app has now been released. Both allow users to register Human IDs, complete basic credential setups, and verify their humanity via palm scans (I’ve actually scanned my palm on the iOS app and the process went smoothly).
- Multi-Tier Verification:
- Email/social ID + wallet reservation (launched May)
- Mobile palm print scan via app (live since mid-June)
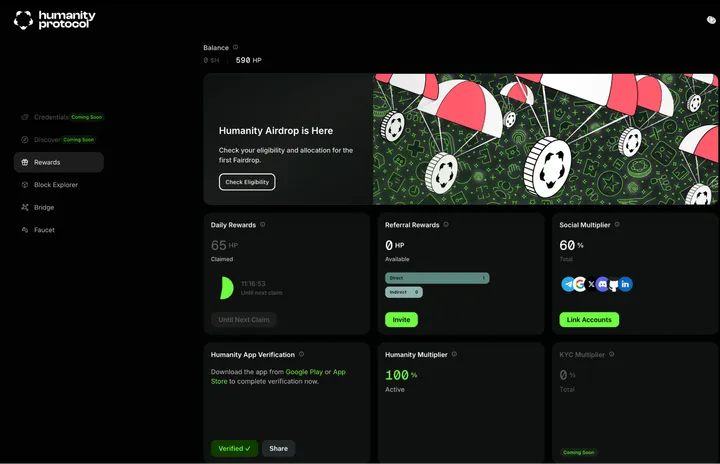
- Testnet Engagement: Over 8 million Human IDs reserved, 10 million wallets registered, and 5 million Humanity Point (HP) holders earning daily testnet rewards. These numbers include duplicate signups across channels (one user can sign up with alternate wallets, social media accounts, or emails). The Humanity dashboard pictured below allows you to track your progress.
Announced Partnerships
- Palm Scans @ ETHCC 2025: Scheduled for August, ETHCC attendees will be able to use Humanity’s palm scan verification system for seamless entry, showcasing the first major deployment in a European setting.
- Moongate: Humanity acquired Moongate in June 2025, gaining access to its event ticketing infrastructure and distribution network. Moongate supports ticketing for ~70% of crypto events. Starting July 2025, it will roll out palm scan access at major events like TOKEN2049, ETHDenver, and Binance Blockchain Week.
- Kaito: Integration of Kaito analytics into verifiable credentials, with 2.2M $H tokens allocated to Kaito’s staking ecosystem
- LayerZero: Enables cross-chain verification of Humanity credentials across Ethereum, Arbitrum, Optimism, and more
- ApeChain: Gaming ecosystem integration using Humanity for Sybil resistance and verified access
- OKX Wallet: Native integration into one of the most widely-used self-custody wallets for testnet participation
- Prenetics (Nasdaq-listed genomics firm): Research collaboration exploring genetic-based identity signals
Fairdrop Announcement
Humanity will soon debut Fairdrops.com, a sybil-resistant airdrop platform. The first campaign, titled the “Humanity Fairdrop,” rewards early testnet users, community contributors, $KAITO stakers, builders, and aligned partners with $H tokens. This distribution campaign is designed to reward early contributors, builders, and community supporters who helped bootstrap the ecosystem.

If you missed this round, more fairdrops are expected.
Future Roadmap Highlights
Humanity’s near-term roadmap reflects a rapid transition from experimentation to production-scale usage. Several high-impact milestones are already in motion or approaching launch:
- Token Generation Event (TGE): The $H token will launch on June 25th, with spot and perps exchange listings including Binance, Bybit, MEXC, and KuCoin. This will mark the beginning of public network participation and token-governed activity.
- zkTLS credentials via browser extension: Humanity is developing a browser extension for self-issued zkTLS credentials, with early use cases expected to include hotel and airline check-ins. This expands the credential format beyond palm scans into everyday digital identity use.
- Specialized palm + vein scanners: Later this year, Humanity will begin distributing custom-built biometric scanners to over 15 countries. These devices enhance accuracy and accessibility for palm-based enrollment and payments.
- Decentralized staking: Users will soon be able to stake $H with validators and zkProofers. This allows non-technical participants to earn rewards passively while supporting credential issuance and verification activity.
- DAO Formation: Humanity DAO is currently in development. Once live, it will give $H holders governance rights over validator rules, treasury decisions, and protocol upgrades.
Each of these developments moves Humanity closer to its goal of becoming a widely adopted, privacy-preserving, and user-owned identity layer.
Risks & Open Questions
Even with demonstrated early momentum and a well-architected system, Humanity faces important unknowns and risks. As with any early-stage infrastructure play, long-term success depends not just on technical execution, but on adoption, incentive alignment, and governance maturity. Below are the key areas that I believe we should pay close attention to:
Opaque Token Allocation Details
While the 29% allocation to early contributors and investors is not inherently unusual for projects at this stage, there is no published vesting schedule or unlock timeline. The lack of public information about tokenomics leaves open questions about near-term sell pressure and long-term contributor alignment.
Additionally, the role of the Human Institute (which holds a separate allocation) remains unclear: how it overlaps with the foundation treasury, why it’s necessary, and what decision-making authority it holds. Until these details are clarified, it’s difficult to assess how governance and treasury control will evolve.
Governance Gaps
Even with a structured governance process outlined, key elements of Humanity’s decentralization roadmap are still undefined.
- No timeline for multisig transition: The Human Institute currently controls the execution multisig and treasury wallets. There is no public information regarding when this control will shift to a broader community-elected group.
- No constraints on emergency powers: While useful for critical patches, the emergency upgrade pathway remains centralized. There are no published safeguards, limits, or transparency requirements around its use.
- No checks on treasury discretion: The Human Institute can currently allocate treasury funds without a binding community vote. Until this changes, meaningful financial control remains centralized.
- No accountability or slashing for multisig operators: The 3-of-5 multisig signers are unnamed and not subject to slashing or term limits. Without formal DAO oversight, trust remains a prerequisite.
Until these issues are addressed, governance decentralization remains aspirational and central control over protocol upgrades, validator rules, and treasury decisions could persist far longer than intended.
Unproven Incentive Models
Last, but certainly not least, Humanity’s business model depends on applications paying to verify credentials, validators earning fees for issuance, and zkProofers being compensated for proof processing. These mechanics are theoretically sound but largely untested.
With exact credential pricing not yet publicly disclosed, it’s unclear what level of network scale will be necessary to create sustainable economics for identity validators and zkProofer nodes. Without meaningful demand from apps and institutions, the system faces the risk of becoming a network of participants generating credentials without real-world utility.
We’ll return to the education example for clarity: if a university is expected to become an identity validator and issue graduation credentials onchain, the cost-benefit must be compelling. They need to be confident that the credential will be widely accepted by employers, that issuance won’t require heavy technical lift, and that they’re being fairly compensated for participating. If these incentives fall short, institutional adoption will lag – and the broader identity ecosystem risks stalling at the proof-of-concept stage.
My Take
Humanity Protocol stands out in the identity landscape not by competing directly with World, but by redefining the market. Where World focuses on vertically integrated hardware + consumer identity, Humanity is composable infrastructure targeting enterprise use cases from day one. Their horizontal scaling strategy, with SDKs and real enterprise integrations, feels far more practically feasible than hardware-bound, consumer-first alternatives.
What encourages me most is that demand already exists and the token actually has utility from day one. Unlike speculative assets waiting for future use, $H is embedded into core protocol flows. That alone gives it a functional foundation most identity tokens never reach.
Privacy-wise, Humanity gets it right: data minimization, flexible opt-ins, and cryptographic guarantees make it sufficient for most users without compromising usability. And the opportunity space it opens (i.e., a decentralized credentialing protocol with real institutional participation) is large. Education, finance, employment, healthcare, and Web3 all need identity rails.
Humanity isn’t playing for a billion-dollar market cap – it’s going after Meta.
That said, success isn’t guaranteed. Governance mechanics, incentive design, and economic sustainability are still unproven. But to me, the core thesis is plausible, demand is visible, and the risk is asymmetric. For now, that’s enough to take Humanity seriously.
0 Comments
